Rangi!
The friendly neighbourhood volcano, and embarking upon a CLR executable metadata jungle expedition

The friendly neighbourhood volcano, and embarking upon a CLR executable metadata jungle expedition

Flat is a project from way back in 2019. The idea was to build a .NET language in Racket, surfacing the Racket macro system alongside a .NET runtime.
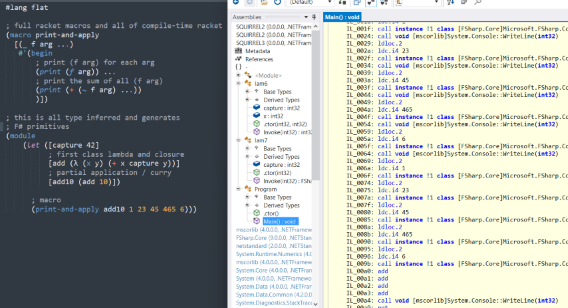
(sorry for the rubbish picture, the scaling killed it)
Today we look at another crackme, SabloomText_v6!
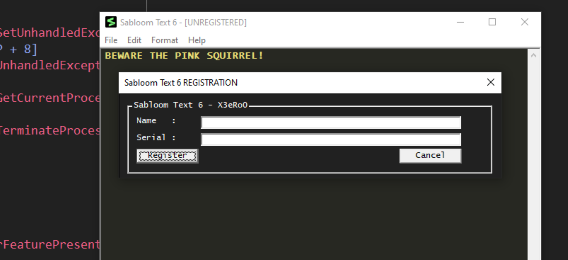
The difficulty is rated at level 4.8 of 6 - I think perhaps it was more like a 4.
I am not going to say anything about it in this section as it would spoil a cool surprise if you want to try it yourself!
Here is the link if you want to try it Sabloom Text 6
Tools used today are x64dbg, PEStudio, F# and C++
(Apologies for the low quality pictures, I messed them up)
In this post we’ll look at another crackme, Bakunawa!
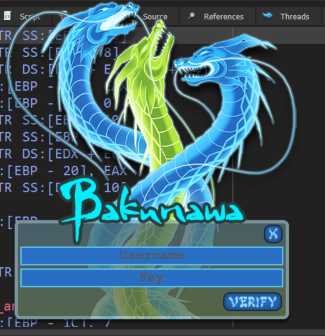
This one was listed as level 5 (Very Hard) and certainly was not without its difficulties!
Featuring a sort-of virtual machine executing real x86 instructions encoded into an odd binary file as a point of obsfucation, this took me quite a long time to figure out. I built some tools in the process and finally a Keygen program once the algorithm was identified and reversed.
Major spoilers follow, here’s the link if you want to have a go yourself!
Tools used today are x64dbg, PEStudio, IDA Pro, F# and C++
In this post we’ll look at the design of a function generator that outputs slope waveforms with adjustable rise and fall times. This can be used in modular synthesis as an envelope, or control voltage to modulate some other parameter in your synthesiser. This post is purely electronics with no CPUs allowed on the scene.
For all the circuits and fragments in this post, I have linked to simulations you can play with. I was going to embed them, but there is no way to prevent all the simulations starting at once and killing your CPU, so I’ll leave it to your discretion :)
In this article we’ll look at another crackme. This one was pretty difficult and has a bunch of cool stuff in it, including the injection and execution of obfsucated code into another process.
In a previous article I described the process of reverse-engineering a crackme. These are programs designed to be broken with various counter-mesaures and challenges. As a break from my hardware work, I thought I would have a go at another one.
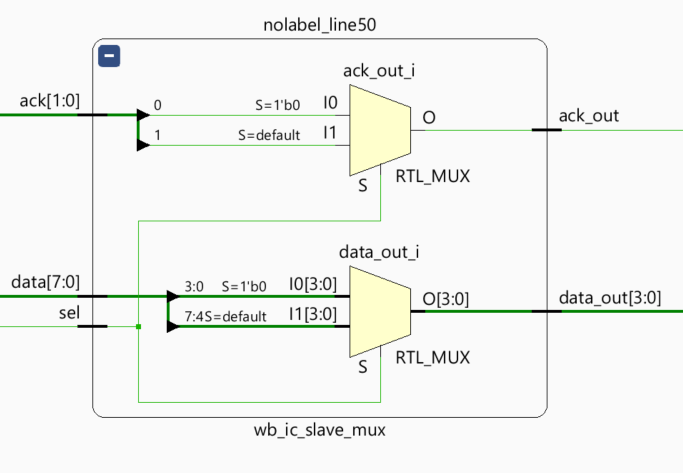
Multiplexers and demultiplexers are common tools in digital logic design. In Verilog, they are fairly simple to create whilst the amount of signals are small. In this post we’ll look at how Fairylog’s macros can make short work of generating mux/demux of any complexity, greatly reducing the amount of work and scope for hard-to-find bugs
Over the last few months I have been working on yet another new language, this time for programming FPGAs. This post will provide a short introduction to Fairylog by way of building some custom hardware to read a pair of Nintendo pads.
Realtime 24bit colour rotozoomer controlled by a NES pad. CPU, video hardware and assembler built in my various @racketlang langs. Display from @adafruit. Debugger and supporting tools #csharp & #fsharp. Complete with dramatic music! 😃 #fpga pic.twitter.com/8gVNfg4uLD
— Ross McKinlay (@pezi_pink) March 7, 2019
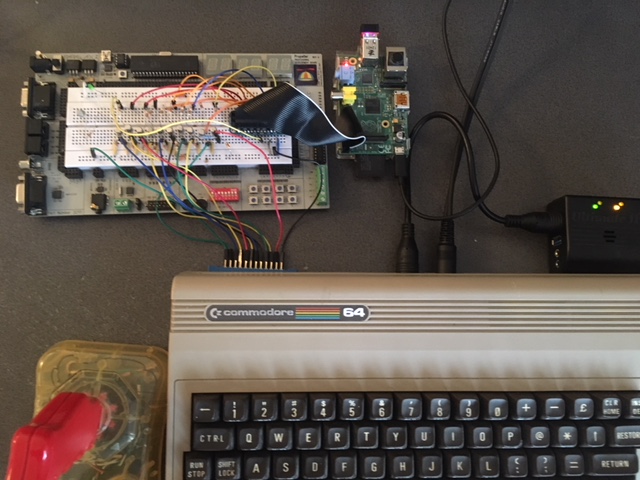
In this post I will describe a small electronics project designed to enable the remote programming of a real Commodore 64 that is switched on and running. To achieve this, several parts are involed, utilising some custom circuitry and communications protocol, a Raspberry Pi, a C program, a 6502 assembler program and a little F# program to finish it off.